Note that this is bit buggy for Fortigate FortiOS 5.2 but works for later versions. Also note that there is an issue with Google Chrome, sometimes allowing google.com even if its supposed to be blocked.
Remember to add EXPLICIT DENY at the end of your list of wildcard sites
==
Does wildcard FQDNs work in policies? The answer is No.
But there is other way to allow wildcards through.
As we all know, Wildcard FQDN firewall address should not be used in a firewall policy (Full details here). Simple explanation is that because the Firewall wont be able to query on to *.example.com when it tests by the policy.
There, however is a workaround. Use WEB-POLICY.
In my scenario, I am controlling what my users will be able to access in the internet. This is a common setup for enterprise networks that uses a Web Proxy to control websites their users can access. I have a few trusted sites that I want my users to access even without a proxy. For the sake of simplicity in example, lets say I am allowing my users to access google.com even without a proxy.
On the policy, we can set an FQDN Address object for every site they can access. But as I mentioned, Wildcard FQDN firewall address should not be used in a firewall policy, therefore you will need to add each and every FQDNs (mail.google.com, maps.google.com, plus.google.com) or if there are too many FQDNs and you dont want to add them one-by-one then apply this workaround.
Note that this is bit buggy for Fortigate FortiOS 5.2 but works well for the later versions.
- Create a new Web Filter Profile. Under Security Profiles -> Web Filter -> Add

2. Give a name to your custom Web Filter.
Tick to enable URL Filter, and populate the list of sites with you wish to allow. In creating an entry for wildacrd, set the type to “Wildcard” and type the URL with asterisk to denote as wildcard, for example, *.google.com. So any sites within the *.google.com such as maps.google.com etc, is covered. Set action to “Allow”.
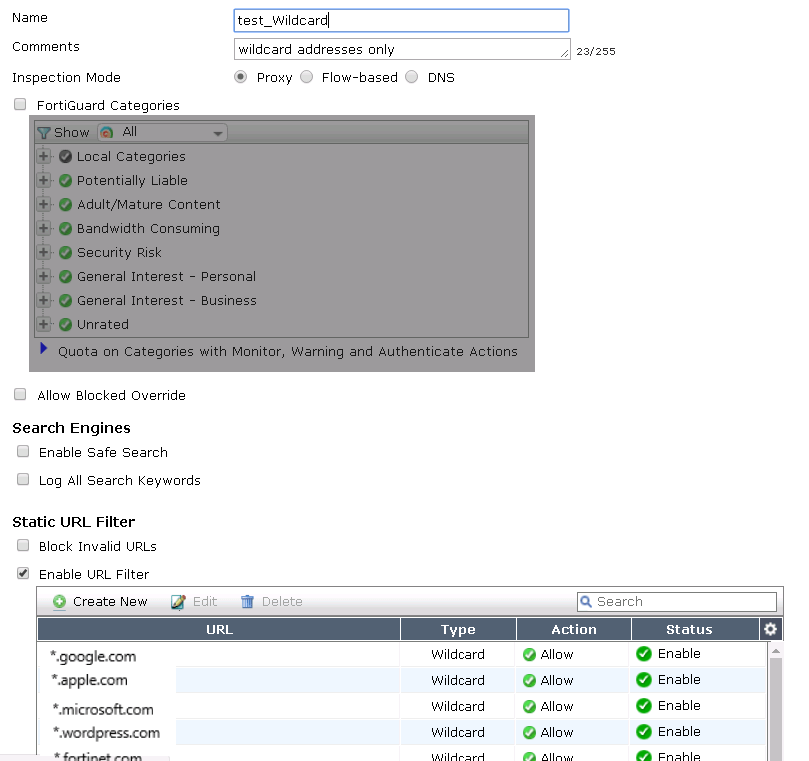
Remember to add a default deny rule at the bottom of the list!
URL = *.*
Type = WIldcard
Action: Deny
3. Set your policy as you would normally set it, make sure to set Service to only “HTTP/HTTPS” (if you are limiting web access like for this example) or also depends on whatever services are you controlling. Set Action to “ACCEPT”. (because obviously if you set it to “Deny” there is no option to set NAT or Web Filter.. 🙂
Then enable Web Filter, and choose the profile you just created.
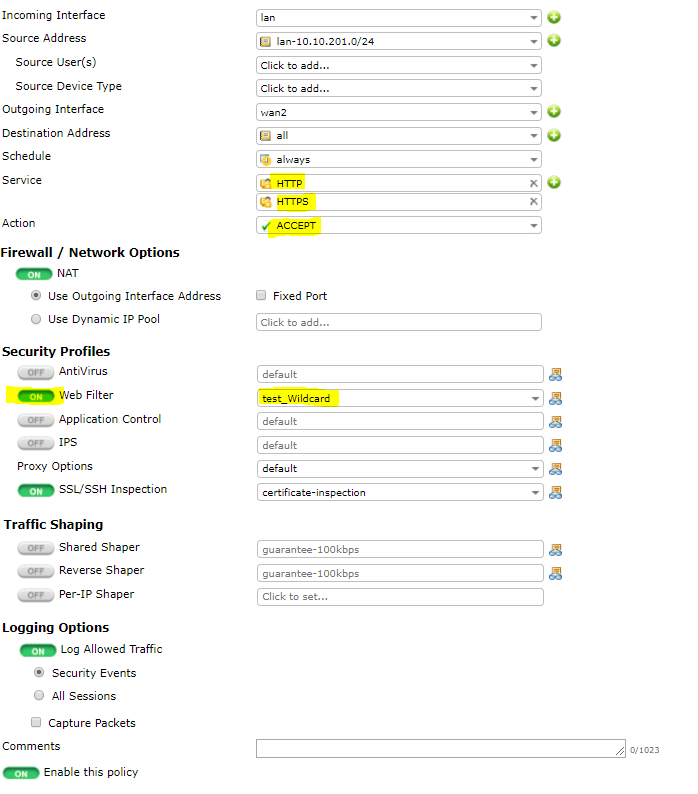
*Best practice, is to create a new object policy for all. and rename it to soemthing like “ALL-with Web Filter” applied so at quick look at the policy it would’nt appear as an allow-all, security Profiles are often overlooked.
4. Make sure you place the Policy at near bottom (as this should be of least priority) so as not to override any other relevant rules, particularly the rule that will allow proxy server to get to the internet. You dont want this rule to match first.
5. Access should now work to the allowed sites (in my case any subdomains within *.google.com) and all others will be denied.
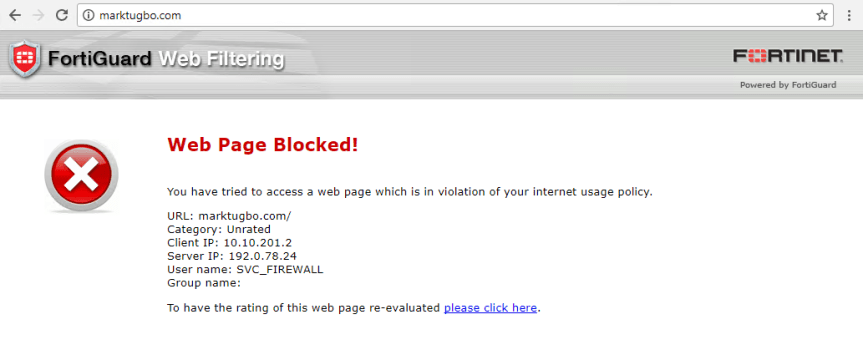
Error page as below when I try to browse some website, not allowed in my policy.


Why are you using fortiguard category filters? Why not turn that off and use an URL filter instead and specify the wildcard in there???
LikeLiked by 1 person
I’m no longer sure where you are getting your info, but great topic. I needs to spend some time finding out much more or working out more. Thanks for wonderful information I used to be looking for this information for my mission.
LikeLiked by 1 person
Great blog here! Additionally your website lots up fast! What host are you the use of? Can I get your affiliate link in your host? I wish my website loaded up as fast as yours lol
LikeLiked by 1 person
DO you know if there is a way to stop telnet connections as well. So for exmple browsing to msn.com is blocked through browser but I am still able to telnet to msn.com on 443
LikeLiked by 1 person
Is the default deny (*.*) still needed in 5.6.x? When I attempt to put that at the bottom of the list in a Static URL filter, when I save the web filter profile, it wipes out all the other entries and leaves me with just the default deny block in the list.
LikeLike
Great news, proper wildcard FQDN addresses support introduced in FortiOS 6.2.2
https://kb.fortinet.com/kb/documentLink.do?externalID=FD48524
LikeLike